- Retrait en 2 heures
- Assortiment impressionnant
- Paiement sécurisé
- Toujours un magasin près de chez vous
- Retrait en 2 heures
- Assortiment impressionnant
- Paiement sécurisé
- Toujours un magasin près de chez vous
Description
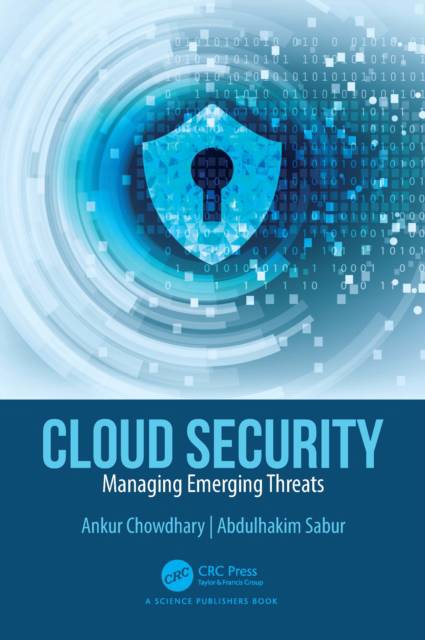
The book reviews the zero-trust model that deviates from the traditional definition of trust boundaries and validates all interactions in a cloud environment. The incident response life cycle is used to prepare for, identify, contain, and eradicate security threats in the cloud. It discusses how automation and autonomous cyber defense tools based on Artificial Intelligence and Machine Learning and techniques can help resourceconstrained security teams address cloud security at a scale. The book also elaborates upon some helpful case studies on the practical deployment of cloud security solutions, their limitations, and lessons learned based on case-studies experience in cloud security.
Spécifications
Parties prenantes
- Auteur(s) :
- Editeur:
Contenu
- Nombre de pages :
- 276
- Langue:
- Anglais
Caractéristiques
- EAN:
- 9781032470788
- Date de parution :
- 02-12-25
- Format:
- Livre relié
- Format numérique:
- Genaaid
- Dimensions :
- 156 mm x 234 mm
- Poids :
- 598 g
Seulement chez Librairie Club
Les avis
Nous publions uniquement les avis qui respectent les conditions requises. Consultez nos conditions pour les avis.