- Retrait en 2 heures
- Assortiment impressionnant
- Paiement sécurisé
- Toujours un magasin près de chez vous
- Retrait gratuit dans votre magasin Club
- 7.000.0000 titres dans notre catalogue
- Payer en toute sécurité
- Toujours un magasin près de chez vous
Description
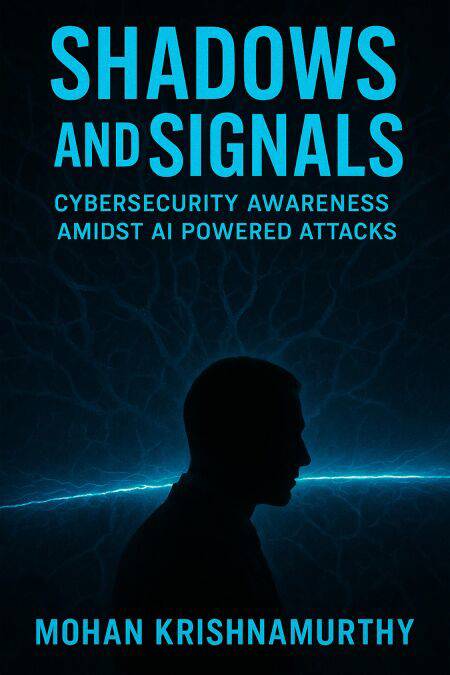
Cyber offense has changed. With AI, attackers compress timelines, personalize lures, and evolve mid-campaign—turning routine business workflows into attack surfaces. Shadows and Signals shows how to retool your organization to win the moment of decision.
What's inside:
AI-Powered Threats, Demystified: Adaptive phishing and BEC 2.0 that pass DMARC, deepfakes/voice clones that collapse informal trust, autonomous ransomware that exfiltrates before encrypting, and API/supply-chain abuse hiding in trusted integrations. Identity is the Perimeter: Passkeys/FIDO2, conditional access, session security, and just-in-time privileges that time-box risk and block lateral movement. Verification Over Intuition: Two-channel callbacks, passphrase challenges, Vendor of Record (VoR) registries, cooling-off periods, and golden paths built directly into ERP/IDP tools. AI for Defense—Done Right: Intent-centric detections, explainable reason codes, safe automation (quarantine, token revoke), and SOC case-building that connects endpoint, identity, cloud, SaaS, and API signals. Governance You Can Operate: AI Use Policy, Model Bill of Materials (MBOM), red-teaming cadence, AI incident response (prompt injection, poisoning, extraction), and third‑party AI due diligence. Culture that Sticks: Role-based micro-learning, champions networks, monthly "Threats We're Seeing," drill design, and recognition programs that reward correct escalation.Actionable assets included:
Playbooks: BEC, OAuth scope governance, exfil intent, privilege elevation anomalies, public share exposure, prompt injection. Metrics & Dashboards: Leading indicators (verification coverage, passkey adoption, OAuth recertification, public share dwell time) and lagging outcomes (MTTD/MTTR, losses prevented). Roadmaps: 90/180/365-day plans to stabilize, harden, and operationalize. Localization (GCC/UAE): PDPL alignment, bilingual templates (Arabic/English), WhatsApp/voice-note norms (no high-risk approvals), and regional workweek/time-zone considerations.Who should read this:
CISOs and security leaders, IT/identity engineers, SOC analysts, finance/AP & treasury teams, operations leaders, product owners embedding AI in workflows, and founders scaling secure-by-design businesses.
Bottom line: You don't need a silver bullet. You need repeatable, explainable systems: identity-centric controls, fast verification protocols, AI-aware detections, and practiced playbooks—measured by the numbers that matter to the business.
Spécifications
Parties prenantes
- Auteur(s) :
- Editeur:
Contenu
- Langue:
- Anglais
Caractéristiques
- EAN:
- 9798224361267
- Date de parution :
- 23-03-26
- Format:
- Ebook
- Protection digitale:
- /
- Format numérique:
- ePub
Seulement chez Librairie Club
Les avis
Nous publions uniquement les avis qui respectent les conditions requises. Consultez nos conditions pour les avis.