- Retrait en 2 heures
- Assortiment impressionnant
- Paiement sécurisé
- Toujours un magasin près de chez vous
- Retrait en 2 heures
- Assortiment impressionnant
- Paiement sécurisé
- Toujours un magasin près de chez vous
Séries : livres de la série Information Security and Cryptography
-
The Science of Quantitative Information Flow
Mário S Alvim, Konstantinos Chatzikokolakis, Annabelle McIver, Carroll Morgan, Catuscia Palamidessi, Geoffrey Smith
- Livre relié | Anglais | Information Security and Cryptography
- This book presents a comprehensive mathematical theory that explains precisely what information flow is, how it can be assessed quantitatively - so br... Savoir plus
64,95 €64,95 € -
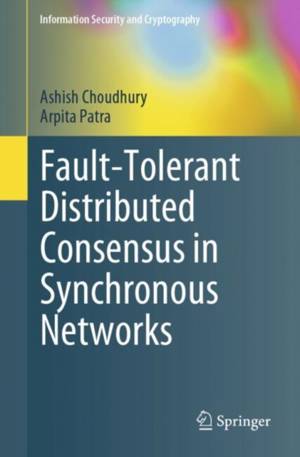
Fault-Tolerant Distributed Consensus in Synchronous Networks
Ashish Choudhury, Arpita Patra
- Livre broché | Anglais | Information Security and Cryptography
- Fault-tolerant distributed consensus is a fundamental concept, both in cryptography as well as distributed computing. Ever since the inception of the ... Savoir plus
129,95 €129,95 € -
Modeling and Analyzing Security Protocols with Tamarin
David Basin, Cas Cremers, Jannik Dreier, Ralf Sasse
- Livre relié | Anglais | Information Security and Cryptography
- The Tamarin prover is an open-source analysis tool for cryptographic protocols. Given a specification of a protocol, possible adversaries, and the des... Savoir plus
58,95 €58,95 € -
The Design of Rijndael
Joan Daemen, Vincent Rijmen
- Livre relié | Anglais | Information Security and Cryptography
- Rijndael was the surprise winner of the contest for the new Advanced En cryption Standard (AES) for the United States. This contest was organized and ... Savoir plus
96,45 €96,45 € -
Towards Hardware-Intrinsic Security
- Livre relié | Anglais | Information Security and Cryptography
- Hardware-intrinsic security is a young field dealing with secure secret key storage. This book features contributions from researchers and practitione... Savoir plus
162,45 €162,45 € -
The Theory of Hash Functions and Random Oracles
Arno Mittelbach, Marc Fischlin
- Livre broché | Anglais | Information Security and Cryptography
- Hash functions are the cryptographer's Swiss Army knife. Even though they play an integral part in today's cryptography, existing textbooks discuss ha... Savoir plus
70,45 €70,45 € -
Introduction to Cryptography
Hans Delfs, Helmut Knebl
- Livre broché | Anglais | Information Security and Cryptography
- The opening section of this book covers key concepts of cryptography, from encryption and digital signatures to cryptographic protocols. Essential tec... Savoir plus
99,45 €99,45 € -
Advanced Statistical Steganalysis
Rainer Böhme
- Livre broché | Anglais | Information Security and Cryptography
- This is the first book dedicated to modern steganography and steganalysis. The author offers a proposal to structure approaches to provably secure ste... Savoir plus
162,45 €162,45 € -
Concurrent Zero-Knowledge
Alon Rosen
- Livre broché | Anglais | Information Security and Cryptography
- Zero-knowledge proofs are fascinating and extremely useful constructs. Their fascinating nature is due to their seemingly contradictory de?nition; ze-... Savoir plus
108,45 €108,45 € -
The Theory of Hash Functions and Random Oracles
Arno Mittelbach, Marc Fischlin
- Livre relié | Anglais | Information Security and Cryptography
- Hash functions are the cryptographer's Swiss Army knife. Even though they play an integral part in today's cryptography, existing textbooks discuss ha... Savoir plus
97,45 €97,45 € -
The Block Cipher Companion
Lars R Knudsen, Matthew Robshaw
- Livre relié | Anglais | Information Security and Cryptography
- This volume provides a detailed account of block cipher analysis, design, and deployment. The authors describe the most prominent block ciphers and gi... Savoir plus
86,95 €86,95 € -
Locally Decodable Codes and Private Information Retrieval Schemes
Sergey Yekhanin
- Livre broché | Anglais | Information Security and Cryptography
- In this book, the author provides a fresh algebraic look at the theory of locally decodable codes and private information retrieval schemes. The autho... Savoir plus
108,45 €108,45 € -
Practical Signcryption
- Livre relié | Anglais | Information Security and Cryptography
- In today's world, data must be sent around the world cheaply and securely, and that requires origin authentication, integrity protection, and confiden... Savoir plus
108,45 €108,45 € -
Introduction to Cryptography
Hans Delfs, Helmut Knebl
- Livre broché | Anglais | Information Security and Cryptography
- The first part of this book covers the key concepts of cryptography on an undergraduate level, from encryption and digital signatures to cryptographic... Savoir plus
54,45 €54,45 € -
The LLL Algorithm
- Livre broché | Anglais | Information Security and Cryptography
- The first book to offer a comprehensive view of the LLL algorithm, this text surveys computational aspects of Euclidean lattices and their main applic... Savoir plus
249,45 €249,45 € -
Fault Analysis in Cryptography
- Livre relié | Anglais | Information Security and Cryptography
- This book covers fault analysis in secret key cryptography, from side-channel analysis and its relevance to fault attacks, to block ciphers, counterme... Savoir plus
108,45 €108,45 € -
Scion: A Secure Internet Architecture
Adrian Perrig, Pawel Szalachowski, Raphael M Reischuk, Laurent Chuat
- Livre relié | Anglais | Information Security and Cryptography
- This book describes the essential components of the SCION secure Internet architecture, the first architecture designed foremost for strong security a... Savoir plus
54,45 €54,45 € -
The Hash Function BLAKE
Jean-Philippe Aumasson, Willi Meier, Raphael C.-W. Phan, Luca Henzen
- Livre relié | Anglais | Information Security and Cryptography
- This is a comprehensive description of the cryptographic hash function BLAKE, one of the five final contenders in the NIST SHA3 competition, and of BL... Savoir plus
92,45 €92,45 € -
Operational Semantics and Verification of Security Protocols
Cas Cremers, Sjouke Mauw
- Livre broché | Anglais | Information Security and Cryptography
- This account of an effective methodology for defining and verifying security protocols in network communication includes an accompanying tool set that... Savoir plus
54,45 €54,45 € -
Cryptography in Constant Parallel Time
Benny Applebaum
- Livre broché | Anglais | Information Security and Cryptography
- This book establishes, for the first time, the potential application of NC O implementations to cryptographic primitives such as one-way functions, ps... Savoir plus
54,45 €54,45 € -
Modelling and Verification of Secure Exams
Rosario Giustolisi
- Livre broché | Anglais | Information Security and Cryptography
- In this book the author introduces a novel approach to securing exam systems. He provides an in-depth understanding, useful for studying the security ... Savoir plus
54,45 €54,45 € -
Guide to Internet Cryptography
Jörg Schwenk
- Livre broché | Anglais | Information Security and Cryptography
- Research over the last two decades has considerably expanded knowledge of Internet cryptography, revealing the important interplay between standardiza... Savoir plus
64,95 €64,95 € -
Fault Analysis in Cryptography
- Livre broché | Anglais | Information Security and Cryptography
- This book covers fault analysis in secret key cryptography, from side-channel analysis and its relevance to fault attacks, to block ciphers, counterme... Savoir plus
108,45 €108,45 € -
Round and Computational Efficiency of Multi-party Protocols
Michele Ciampi, Luisa Siniscalchi
- Livre relié | Anglais | Information Security and Cryptography
- Cryptographic protocols are the backbone of secure digital interactions, but achieving both security and efficiency is a challenging balancing act. Th... Savoir plus
213,95 €213,95 €